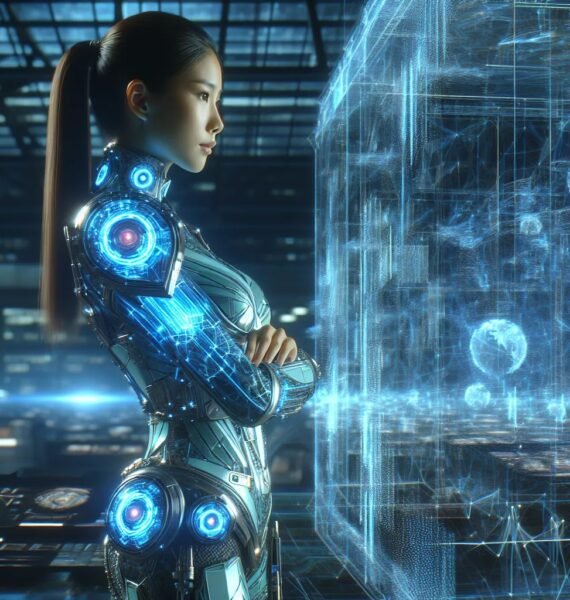
Cyber Security & IT Management
Lorem ipsum dolor sit amet, consectetur adipiscing elit, sed do eiusmod tempor incididunt ut labore et dolore magna aliqua. Quis ipsum suspendisse ultrices gravida.
Cyber Security Is Not Optional
Lorem ipsum dolor sit amet, consectetur adipiscing elit, sed do eiusmod tempor incididunt ut labore et dolore magna aliqua. Quis ipsum suspendisse ultrices gravida.
High-Performance Solutions
Lorem, ipsum dolor sit amet consectetur adipisicing elit. Doloribus quam neque quibusdam corrupti aspernatur corporis alias nisi dolorum expedita veritatis voluptates minima sapiente.
Threat Hunter — Proactive Threat Hunting & Detection Engineering
We combine automated discovery with deep manual verification to eliminate false positives and to uncover complex chains of exploitation
Read More
Incident Responder — Rapid, Expert Cyber Incident Response
Protecting critical systems by rapidly detecting, containing, and remediating breaches with expert forensics, threat hunting, and incident coordination.
Read More
Secure Managed IT
Why Secure Managed IT Matters
In a landscape of persistent threats and growing operational complexity, organizations need IT that not only runs reliably but also defends proactively.

Compliance
Demonstrable compliance is essential — it enables trust, market access, and resilience. Embed compliance into engineering and operations, automate evidence collection.
Read More
Disaster Planning — Comprehensive Cyber Disaster Recovery & Business Continuity
Ensuring business continuity through risk assessments, prioritized recovery plans, regular backups, and tested incident-runbooks for swift restoration.
Read More
Secure By Design — Security-First Architecture & Engineering
We embed security into the full software and system lifecycle, delivering secure-by-design architectures, threat-informed engineering, and developer-focused controls that reduce risk without slowing delivery.
Read More

Transform Your Digital Workflow Be Productive Reduce Risk
Lorem ipsum dolor sit elit amet, consectetur adipiscing elit, sed do eiusmod tempor incidiunt labore et dolore magna aliqua. Quis ipsum suspendisse Workflow Be productive consectetur adipiscing
Development
Design
Marketing
Buy Our Plans & Packages Monthly
Lorem, ipsum dolor sit amet consectetur adipisicing elit. Doloribus quam neque quibusdam corrupti aspernatur corporis alias nisi dolorum expedita veritatis voluptates minima sapiente.
One Time
Free / Per Month
- The Departure Of The Expect
- Remote Administrator
- Configure Software
- Special Application
- 24/7 Support
Business
$70 / Per Month
- The Departure Of The Expect
- Remote Administrator
- Configure Software
- Special Application
- 24/7 Support
Exclusive
$120 / Per Month
- The Departure Of The Expect
- Remote Administrator
- Configure Software
- Special Application
- 24/7 Support

Why Choose Us
Lorem ipsum dolor sit amet, consectetur adipiscing elit, sed do eiusmod tempor incididunt ut labore et dolore magna aliqua. Quis ipsum suspendisse ultrices gravida. Risus commodo viverra maecenas accumsan lacus vel.
- Extemly low response time at all time
- We are always ready for your growth
- We understand security and compliance
Vaximo Recent Services
Lorem, ipsum dolor sit amet consectetur adipisicing elit. Doloribus quam neque quibusdam corrupti aspernatur corporis alias nisi dolorum expedita veritatis voluptates minima sapiente.
Policy Development & Compliance — Governance, Policies, and Audit-Ready Controls
We create tailored policy frameworks and compliance programs that translate regulatory requirements and security strategy into implementable, auditable policies, procedures,
Read MoreCyber Training & Awareness Role‑Based Security Education and Behavior Change
Full-scope adversary emulation: from reconnaissance through persistence and exfiltration.
Read MoreCyber Threat Intelligence & Monitoring — Actionable Intelligence and Continuous Detection
Comprehensive CTI and monitoring services that combine strategic threat intelligence, tactical indicators, and continuous telemetry monitoring to reduce risk.
Read MoreTailored Cyber Solutions for Your Business
Global IT ecosystems are more complex than ever. Cloud-native applications, microservices, distributed workforces, IoT endpoints, and third-party integrations expand the attack surface
Read MoreData Encryption — Robust Cryptography for Confidentiality, Integrity & Compliance
We design and implement enterprise-grade encryption strategies that protect data at rest, in transit, and in use, ensuring confidentiality, integrity, and regulatory compliance while enabling practical operations.
Read MoreEndpoint Security — Advanced Endpoint Protection & Response
Comprehensive endpoint security services combining prevention, detection, and response to protect desktops, laptops, servers, containers, and IoT devices against modern threats.
Read More
Cyber Security Satistics Graph
Lorem ipsum dolor sit amet, consectetur adipiscing elit, sed do eiusmod tempor incididunt ut labore et dolore magna aliqua. Quis ipsumv
Lorem ipsum dolor sit amet, consectetur adipiscing elit, sed do eiusmod tempor incididunt ut labore et dolore magna aliqua. Quis ipsum suspendisse ultrices gravida. Risus commodo viverra maecenas accumsan lacus vel.
15 Ways To Protect Your Bussiness From A Cyber Attack
DownloadFrequently Asked Questions
Lorem ipsum dolor sit amet, consectetur adipisicing elit. Impedit, libero harum cum numquam repellendus autem recusandae voluptatem, asperiores iusto magni reprehenderit.

-
What's The Difference Between IDS And IBS?
Lorem, ipsum dolor sit amet How do you Startup? consectetur adipisicing elit. Accusamus ipsa error, excepturi, obcaecati aliquid veniam blanditiis quas voluptates maxime unde, iste minima dolores dolor perferendis facilis. How do you Startup blanditiis voluptates Lorem, ipsum dolor sit amet How do you Startup amet How do.
-
How Is Encryption Different From Hacking?
Lorem, ipsum dolor sit amet How do you Startup? consectetur adipisicing elit. Accusamus ipsa error, excepturi, obcaecati aliquid veniam blanditiis quas voluptates maxime unde, iste minima dolores dolor perferendis facilis. How do you Startup blanditiis voluptates Lorem, ipsum dolor sit amet How do you Startup amet How do.
-
What Is Firewall And Why It Is Used?
Lorem, ipsum dolor sit amet How do you Startup? consectetur adipisicing elit. Accusamus ipsa error, excepturi, obcaecati aliquid veniam blanditiis quas voluptates maxime unde, iste minima dolores dolor perferendis facilis. How do you Startup blanditiis voluptates Lorem, ipsum dolor sit amet How do you Startup amet How do.
-
What Steps Will You Take To Secure Server?
Lorem, ipsum dolor sit amet How do you Startup? consectetur adipisicing elit. Accusamus ipsa error, excepturi, obcaecati aliquid veniam blanditiis quas voluptates maxime unde, iste minima dolores dolor perferendis facilis. How do you Startup blanditiis voluptates Lorem, ipsum dolor sit amet How do you Startup amet How do.
What Client’s Say About Us
Lorem, ipsum dolor sit amet consectetur adipisicing elit. Doloribus quam neque quibusdam corrupti aspernatur corporis alias nisi dolorum expedita veritatis voluptates minima.
Lorem ipsum dolor sit amet, consectetur adipiscing elit,do eiusmod tempor incididunt ut labore et dolore.

Kilva Dew
DeveloperLorem ipsum dolor sit amet, consectetur adipiscing elit,do eiusmod tempor incididunt ut labore et dolore.

Axon Detos
CEOLorem ipsum dolor sit amet, consectetur adipiscing elit,do eiusmod tempor incididunt ut labore et dolore.

John Dona
DesignerLorem ipsum dolor sit amet, consectetur adipiscing elit,do eiusmod tempor incididunt ut labore et dolore.

Jon Smith
DeveloperLorem ipsum dolor sit amet, consectetur adipiscing elit,do eiusmod tempor incididunt ut labore et dolore.

Alien Dew
ManagerLorem ipsum dolor sit amet, consectetur adipiscing elit,do eiusmod tempor incididunt ut labore et dolore.

Alen Meair
ReviewerLatest News From Blog
Lorem, ipsum dolor sit amet consectetur adipisicing elit. Doloribus quam neque quibusdam corrupti aspernatur corporis alias nisi dolorum expedita veritatis voluptates minima sapiente.